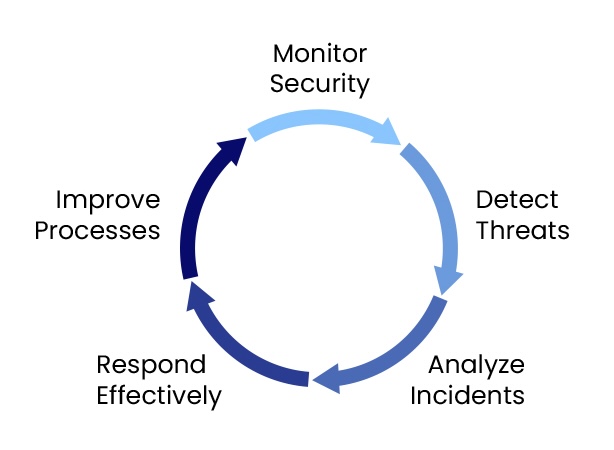
SOC operations focus on continuously identifying, investigating, and responding to potential security incidents.

Continuous Monitoring: Ongoing surveillance of all security systems to detect anomalous activity.
Incident Response: Prompt action to contain and remediate security breaches.
Alert Triage: Identifying and filtering false positives from genuine alerts.
Threat Intelligence: Collecting and sharing information on emerging threats.
Security Incident Management: Ensuring incidents are handled effectively and efficiently, with proper escalation procedures.
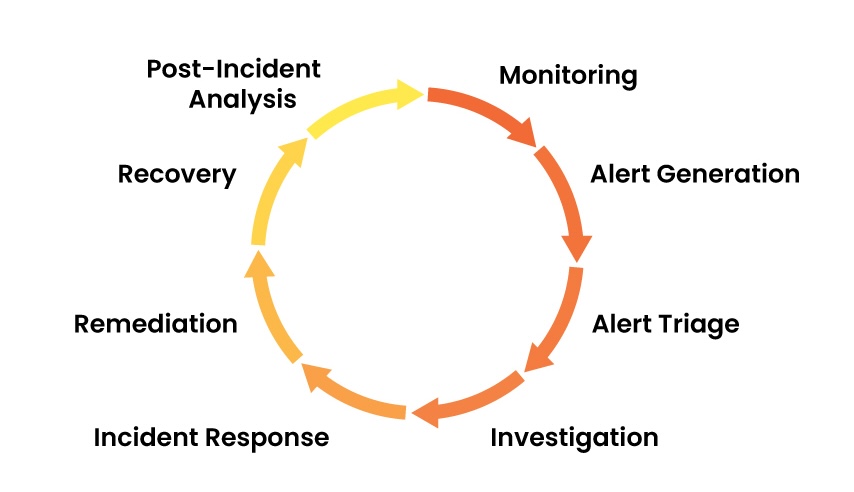
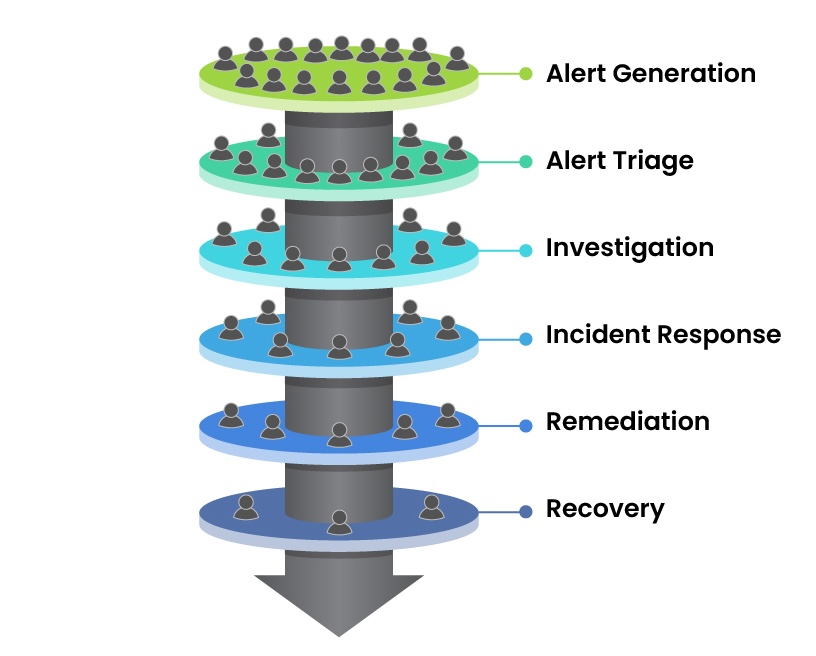
Alert Generation: The monitoring tools detect unusual activities or events and generate alerts.
Alert Triage: Analysts review and assess the severity of alerts.
Investigation: Analysts dig deeper into the alert to determine its legitimacy.
Incident Response: Once a genuine threat is identified, response measures such as isolation or blocking IPs are taken.
Remediation: Infected systems are cleaned or patched to prevent further damage.
Recovery: Systems are restored to normal functionality, and monitoring continues.
Post-Incident Analysis: Analysts investigate the root cause and document findings for future prevention.
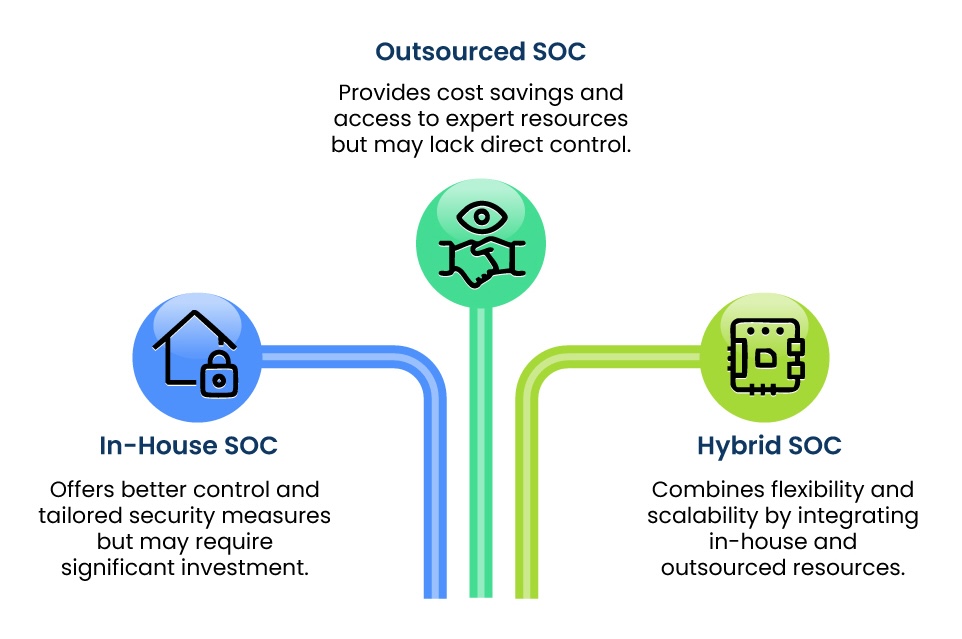
In-House (Internal) SOC: Managed and operated within the organization. Offers better control and tailored security measures.
Outsourced SOC: A third-party vendor manages the SOC. Useful for cost savings and access to expert resources.
Hybrid SOC: Combines in-house SOC with outsourced resources for flexibility and scalability.
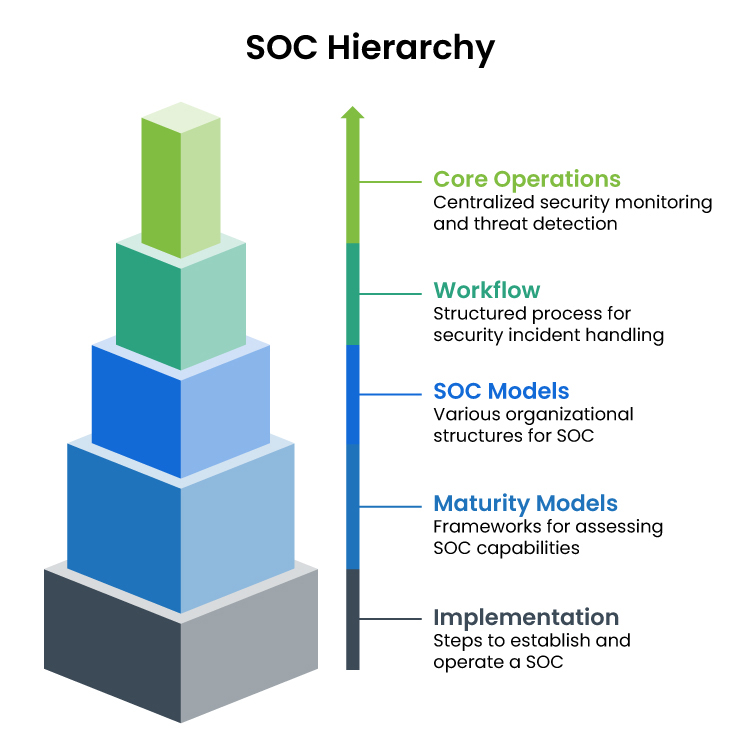
Maturity Models
Maturity models assess the progression and capabilities of a SOC. The SOC Capability Maturity Model includes various stages.
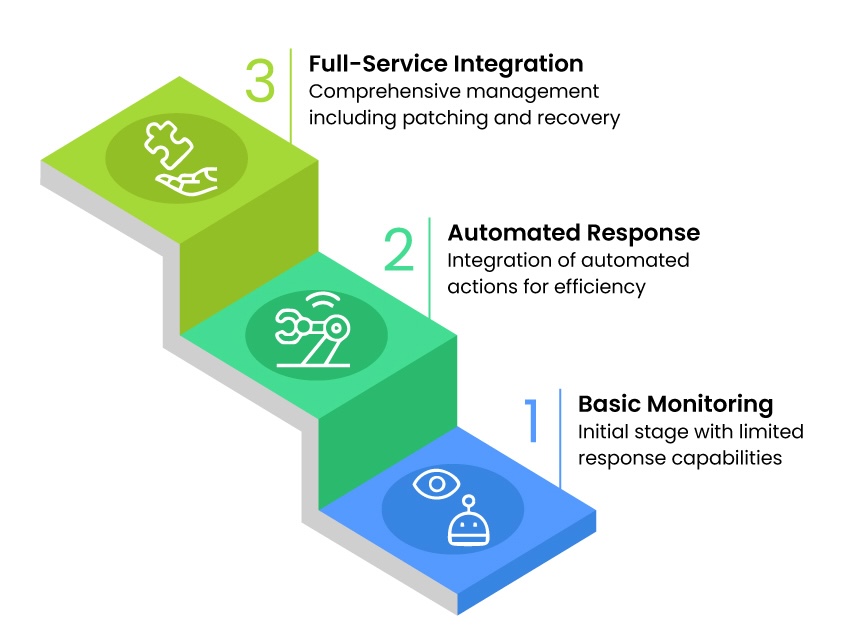
Maturity Level 1: Basic monitoring with limited response capabilities. Correlation rules are created.
Maturity Level 2: Automated response actions are integrated to improve efficiency.
Maturity Level 3: Full service management integration, including patching, recovery, and post-incident processes.
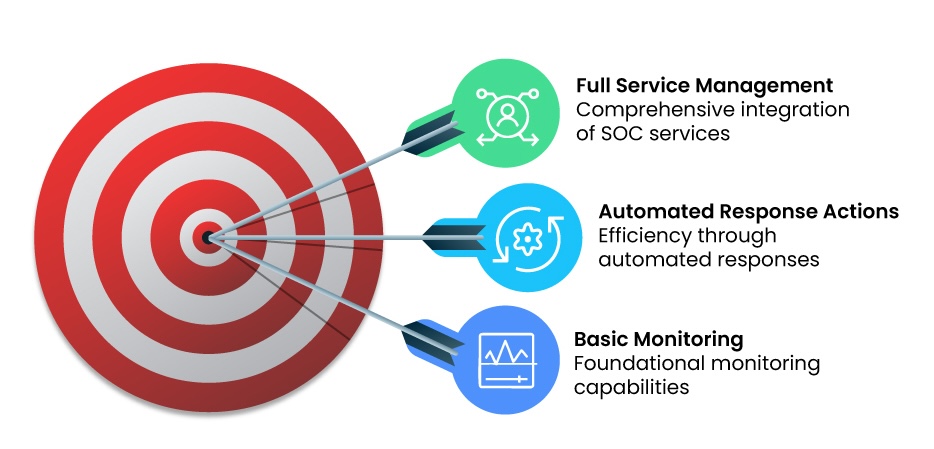
Maturity Models
Maturity models assess the progression and capabilities of a SOC. The SOC Capability Maturity Model includes various stages.
Implementing a SOC involves:
Planning and Design: Understanding the organization's security needs and designing a framework.
Resource Allocation: Identifying technology, staff, and other resources needed.
Deployment: Installing and configuring security tools and processes.
Monitoring and Optimization: Ongoing tuning of detection capabilities and response processes.
Contact us to learn more. Call +91 44 6669 2727 or Email ks-info@kryasolutions.com
Download Brochure